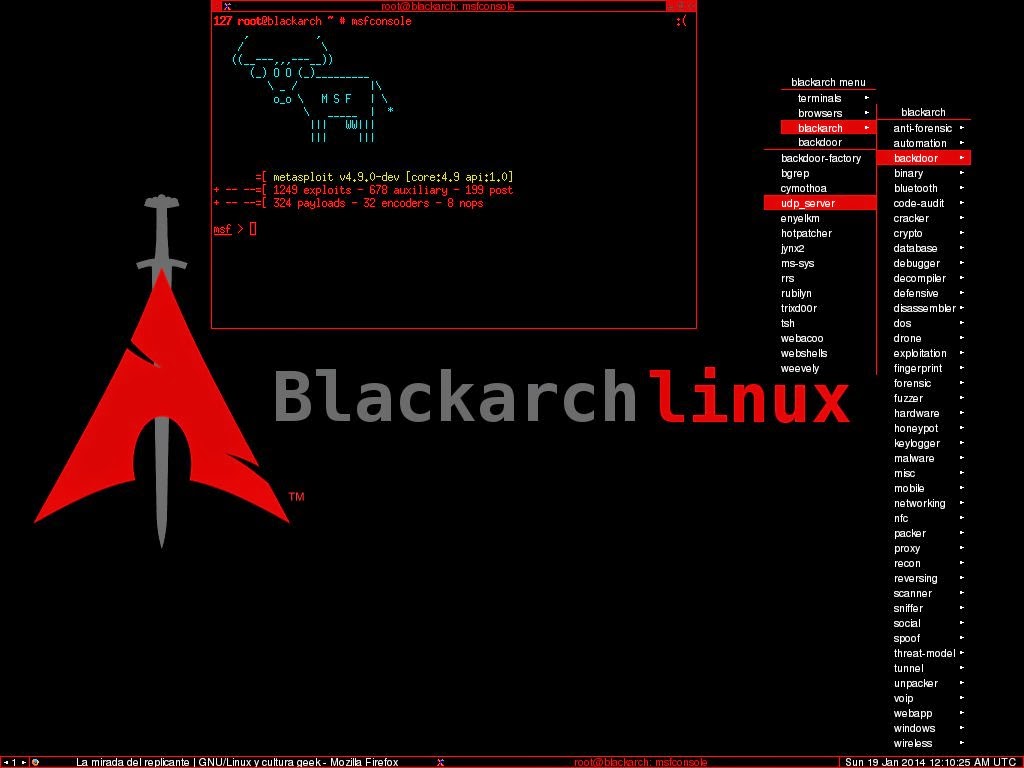
BlackArch Packages
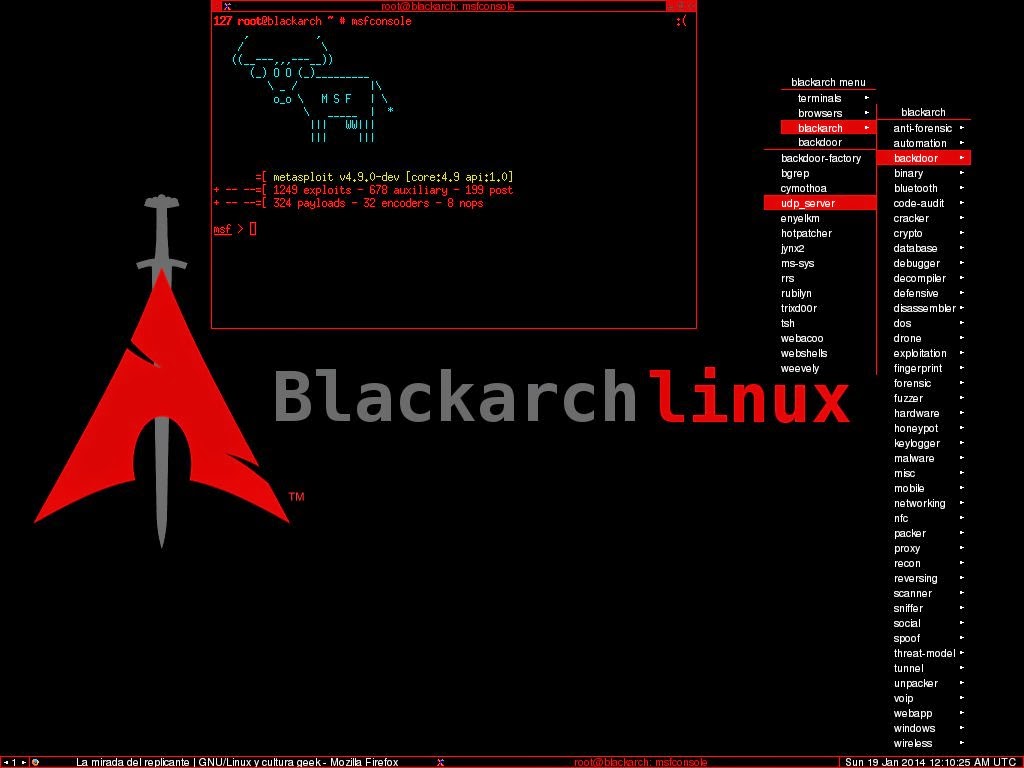
BlackArch Linux is a penetration testing distribution based on Arch Linux that provides a large collection of security and hacking tools. The BlackArch repository contains over 2600 tools that can be installed individually or in groups. The tools are organized into categories to make it easier for users to find what they need. Here are some of the categories and examples of tools available in the BlackArch repository:
-
Information Gathering:
- theharvester: E-mail, subdomain, and people names harvester
- recon-ng: Full-featured web reconnaissance framework written in Python
-
Vulnerability Assessment:
- openvas: Open Vulnerability Assessment Scanner
- nikto: Web server scanner
-
Exploitation Tools:
- metasploit: Penetration testing platform
- armitage: A graphical cyber attack management tool
-
Post Exploitation:
- powersploit: PowerShell Post-Exploitation Framework
- mimikatz: A little tool to play with Windows security
-
Wireless Attacks:
- aircrack-ng: A set of tools for auditing wireless networks
- reaver: Brute force attack tool against Wi-Fi Protected Setup (WPS)
-
Web Application Analysis:
- burpsuite: An integrated platform for performing security testing of web applications
- zaproxy: OWASP ZAP (Zed Attack Proxy)
-
Forensics:
- autopsy: A graphical interface to The Sleuth Kit for digital forensics
- volatility: An advanced memory forensics framework
-
Social Engineering:
- setoolkit: Social Engineering Toolkit
- ettercap: A comprehensive suite for man-in-the-middle attacks
-
Sniffing & Spoofing:
- wireshark: A network protocol analyzer
- bettercap: The Swiss Army knife for 802.11, BLE, IPv4, and IPv6 networks reconnaissance and attacks
-
Password Attacks:
- john: John the Ripper password cracker
- hashcat: World's fastest and most advanced password recovery utility
These are just a few examples, and there are many more tools available in the BlackArch repository. Keep in mind that using these tools for unauthorized activities is illegal and unethical. Ensure that you have the proper authorization before using any penetration testing tools.
Thank you.