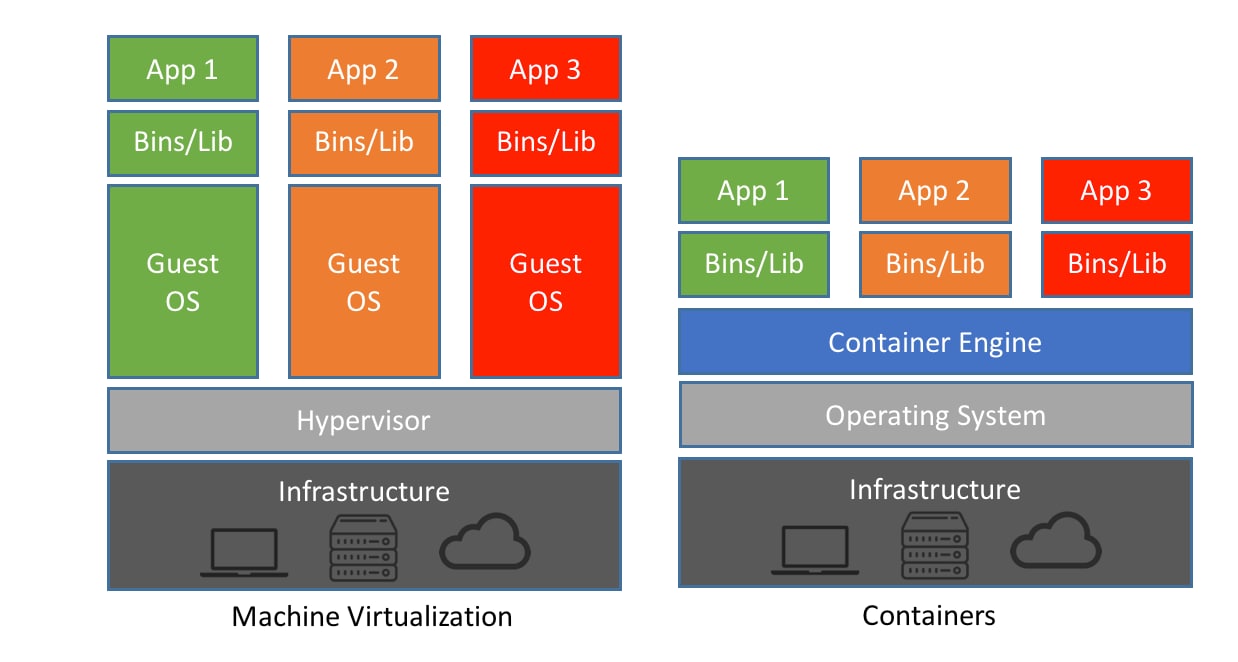
Containers within virtual machines (VMs) refer to the practice of running containerized applications and workloads inside a virtual machine. This approach combines the benefits of both virtualization and containerization technologies and is often used in scenarios where additional isolation and security are required.
Here's an Explanation of Containers in a VM:
Virtual Machines (VMs):
Containers:
Containers within VMs:
a. Isolation: VMs provide strong isolation between workloads. Running containers within VMs can offer an additional layer of security and isolation, making it suitable for multi-tenant environments or when the workloads have different security requirements.
b. Compatibility: Some legacy applications or operating systems may not be well-suited for containerization. Running these applications in VMs while deploying newer containerized applications on the same hardware can maintain compatibility.
c. Resource Allocation: VMs allow you to allocate specific resources, such as CPU, memory, and storage, to each containerized workload. This can be useful for ensuring resource guarantees and limiting the impact of one container on others.
d. Networking: VMs provide network isolation, allowing you to configure network settings independently for each VM running containers. This can be advantageous for complex networking configurations or scenarios requiring multiple separate network spaces.
e. Management and Orchestration: VM orchestration platforms like VMware vSphere or OpenStack can be used to manage both VMs and containers, providing a unified management and security model.
f. Hybrid Environments: Organizations with both VM and container workloads might choose to run containers within VMs as part of a transition strategy or to maintain compatibility with existing VM-based infrastructure.
Containers within VMs offer flexibility and security, but they come with a slightly higher overhead compared to running containers directly on a host operating system. The choice between running containers in VMs or directly on a host OS depends on your specific use case, security requirements, and resource allocation needs.
Thank you.